Let's discuss 2-Factor Authentication
Using another factor of verification besides a password, allows you to have an extended layer of security.
Passwords are the most common and fundamental means of authentication in most services on the internet. You provide your password, let’s say, to a web application to verify who you claim to be. But what if somebody had your password and claimed to be you? So, assuming your password could be hacked, why not have another factor that helps an application verify it is indeed you?
💡Using another factor of verification besides a password, allows you to have an extended layer of security. It helps in preventing your account from being compromised even if your password is somehow breached or hacked by a malicious user.
🎥FourZeroThree - YouTube
Heads up! Did you know I also run a YouTube channel by the same name “FourZeroThree”? I try to create short and entertaining videos out of the articles I post. Don’t forget to check it out!
Understanding the basics of Multi-Factor Authentication (MFA)
Multi-factor Authentication (MFA), as the name explains, is having multiple factors that help verify who you claim to be. There are 3 types of factors that can do so.
Something you know - This verification factor is something that you commit to memory, like your password, PIN, or security questions.
Something you have - This verification factor is something you possess. This could be your mobile device or a device like an RSA SecurID or a Yubi key.
Something you are - This verification factor is something unique to your body, such as your fingerprint.
An application is said to have MFA if it employs either two or all types of authentication factors mentioned above (basically, more than one type of authentication). Most web applications, however, usually employ the first two factors - something you know and something you have. Hence MFA in such applications is more often termed 2-Factor Authentication (2FA).
2-Factor Authentication
Most web applications employ the “something you have” factor as the second factor of authentication - mostly verifying you with your mobile device. Here are some of the methods web applications employ as the second factor of authentication (something you have).
One-time passwords (OTP) via SMS sent to your mobile number.
Soft tokens or Time-based one-time passwords (TOTP) generated by mobile applications (software) like Google Authenticator & Authy.
Hard tokens (TOTPs), generated by devices (hardware) like an RSA SecurID.
Universal 2nd Factor abbreviated as U2F is an open authentication standard used by specialized USB devices like a Yubikey.
One-time passwords (OTP) via SMS
This is often the most employed means of 2nd-factor authentication by websites/applications/services. You feed in your phone number to the application and activate 2FA for your account. Whenever you log in, the application will send an OTP to your mobile number via SMS, to verify it is you logging in. Simple and straightforward.
It’s easy to use, and best of all has minimal risk of locking you out even if you lose your device (you could always contact your mobile network operator to issue another sim card with the same number and use it with another device).
Soft tokens or Time-based one-time passwords (TOTP)
Now, while OTP via SMS is convenient, it has received a lot of flak over the years. Using a TOTP via mobile applications like Google Authenticator or Authy for 2FA has become popular. Using soft tokens for 2FA is more secure than OTPs received via SMS.
If a website, say, for example, Twitter offers setting up 2FA for your account with soft tokens, it would ask you to scan a bar code/QR code through your phone camera (via the “scan a bar code” option in the Authenticator app), so it could register your account for 2FA.
The Authenticator app then generates a TOTP for that particular Twitter account. A new 6 digit code (TOTP) is generated every 30 seconds.
Whenever you log in, unlike the SMS - OTP based 2FA, you don’t have to wait for a code to be generated, new codes are generated continuously every 30 seconds. You open the Authenticator app on your mobile and copy the TOTP.
You could watch this video to get an idea of how you could use Google Authenticator for 2FA. Also, Authy has a great blog and support website with tons of articles for you to read and learn from.
Lose or conk your device and you are locked out of your account. Usually, services provide secret backup codes (that you could use only once) for you to copy, when you activate soft token 2FA. You could use backup codes when you don’t have your device.
Hard tokens
Unlike a mobile application generating codes (tokens) for you, you have a special device that does the job. RSA SecurID is one such device. Like a TOTP generating app, the RSA SecurID generates a new 6 digit TOTP every 30 seconds.

The biggest disadvantage is that an RSA device can be used as a means of 2FA for only one service/application. You would have to buy multiple devices corresponding to the number of services you use. Also, not many services support an RSA device. Nope, not very practical.
Universal 2nd Factor (U2F)
U2F devices like a Yubikey is a specialized USB device, that you could simply plug into your device (like your laptop), to authenticate you to a service. Usually, a device like Yubikey is also classified as a hard token. Troy Hunt has written an article on how this device can be used. If you are the visual kind, you could watch this video.
Hardware devices like RSA SecurID or Yubikey, like your soft token 2FA, have the disadvantage of locking you out if you lose your device. Store your backup codes safely.
🤔Isn't a password enough for account hygiene & security?
I am afraid, an account protected by password only, may not be enough security for your account. Let’s analyze why.
Let’s be real, we are humans after all. What you think is a complex password may well be brute-forced by a tool or script.
The only secure password is the one you can’t remember
- Troy Hunt
Malicious cybercriminals are incessantly trying to find ways to breach websites. Some big names that were breached in the past include Linkedin, Quora, Zomato, Equifax, Dubsmash, Zynga, Yahoo, and many more. This, coupled with insecure practices like using the same password more than once (or worse - all the time) is a reason enough to use 2FA.
Your email address is sensitive and is very important to protect, especially if you primarily use a single email address to sign up everywhere. Most websites/applications use services like email, to help reset passwords. If your email is hacked, it is game over! Irrespective of whether you use 2FA for other services, for god’s sake protect your email additionally with 2FA.
Another reason why you should use 2FA —> This is what Google’s security research (in 2019) reported on account hygiene 👇
We found that an SMS code sent to a recovery phone number helped block 100% of automated bots, 96% of bulk phishing attacks, and 76% of targeted attacks. On-device prompts, a more secure replacement for SMS, helped prevent 100% of automated bots, 99% of bulk phishing attacks and 90% of targeted attacks.
Is it possible for a hacker to bypass 2FA?
Though technically possible, the odds of that happening are remote. Here are some possibilities.
Drawbacks of 2FA depending on SMS and Soft tokens
Attackers could make use of SIM-swapping to port the victim’s mobile number to their device. Doing so would redirect OTPs to the attacker’s device. This article reported in Times of India explains a real-life example of how an Insurance Executive in Bangalore, India, had fallen prey to this attack.
Malicious actors could exploit flaws in mobile networks to intercept text messages.
NIST is no longer recommending two-factor authentication systems that use SMS, because of their many insecurities.
- Bruce Schneier
Reddit Breach Highlights Limits of SMS-Based Authentication
“Already having our primary access points for code and infrastructure behind strong authentication requiring two factor authentication (2FA), we learned that SMS-based authentication is not nearly as secure as we would hope, and the main attack was via SMS intercept,” Reddit disclosed.
“We point this out to encourage everyone here to move to token-based 2FA.”
- Krebs on Security
Both SMS and TOTP generating apps like Authy generate a one time 6 digit code. These codes, like passwords, can be phished too. Here is an excerpt from Bruce Schneier’s blog post “Real-Time Attacks Against Two-Factor Authentication”.
When targets entered passwords into a fake Gmail or Yahoo security page, the attackers would almost simultaneously enter the credentials into a real login page. In the event targets' accounts were protected by 2fa, the attackers redirected targets to a new page that requested a one-time password. This isn't new. I wrote about this exact attack in 2005 and 2009.
A similar attack was explained in the podcast “What kind of idiots get phished?”.
And, when you put in your (victim) username and your password on his (attacker’s) page (phishing page), he just immediately forwarded that to a real Gmail login. And from there, because he (attacker) put in your username and password, a two-factor code was texted to you (victim).And, when you (victim) then put that again into his (attacker’s) fake page, he immediately put that into the real Gmail login page and he was completely into your Gmail. And the server he was using was actually based in New York, so if you check where you’ve recently signed into Gmail, it will show a New York-based location…
By tricking you into installing malware on your mobile device, attackers could get hold of the 2FA codes, be it via SMS or TOTP generating apps.
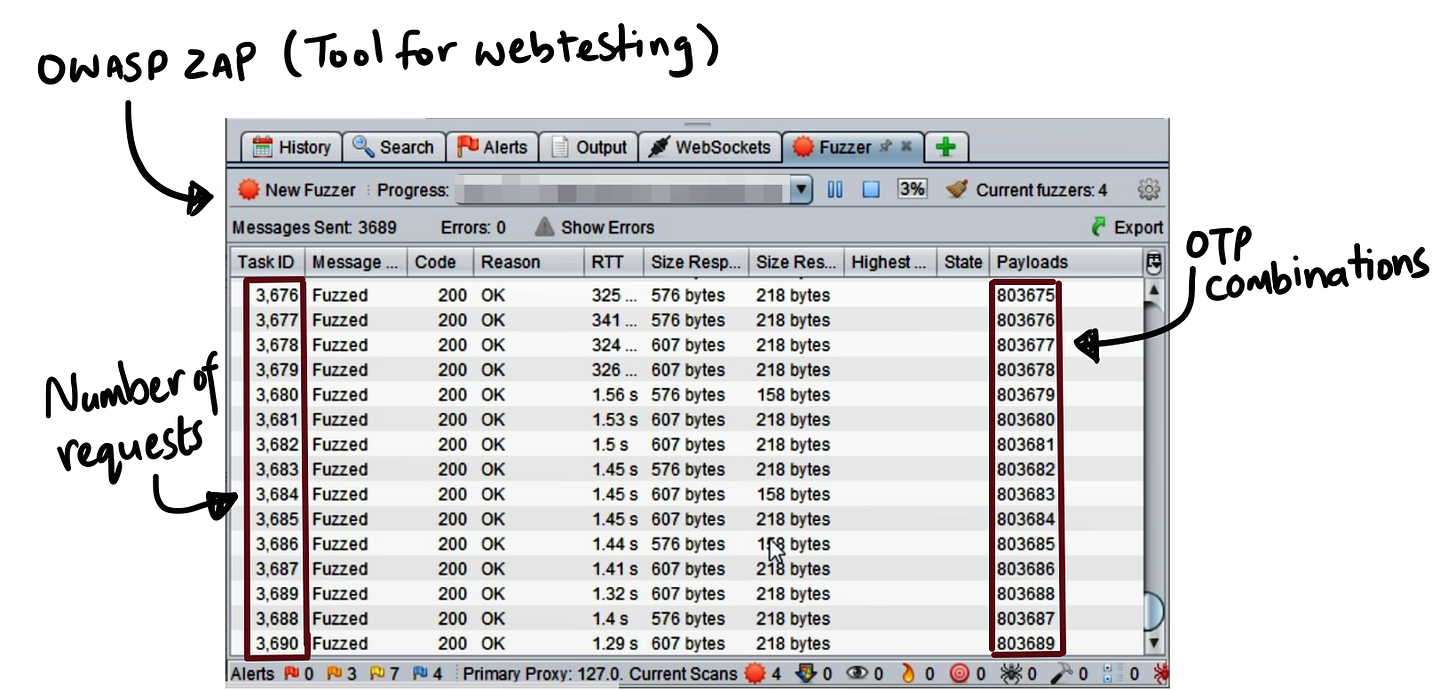
Brute-forcing the 6 digit OTP/TOTP.
OTPs/TOTPs are usually 6 digit codes that could range from 000000 to 999999. Hence the code is a number within 1 million combinations. Attackers could use tools that help generate numerous requests and guess the OTP/TOTP by brute-force, in a few minutes.
However, TOTPs change every 30 seconds, and the chances of success are very slim. OTPs received via SMS, on the other hand, are relevant for a longer period, at least 15 minutes at times, which is enough time for a successful attack to be executed.
A brute-force attack, however, is usually mitigated by the web application/service, by either blocking the account after a minimum number of requests (3-10 requests) or throttling the number of requests (with Captcha, for example).
So, a time constraint, along with the website’s mitigation of blocking or throttling requests, could make it hard to execute a successful attack.
Drawbacks of web applications/services having a vulnerable 2FA feature
Sometimes, the problem lies in the web application offering a 2FA service. If there is a security vulnerability/bug or a flaw in the design of a 2FA set up in the web application, hackers can find ways to bypass 2FA.
Closing Notes
Don’t be lazy. Secure your account with a 2FA wherever possible, especially your email, banking, shopping, and social media accounts.
In the spectrum of the “something you have” verification factors (usually adopted by most applications), SMS would be the least secure and a U2F device like the Yubikey would be the most secure 2nd factor. Soft tokens lie in the soft spot of being more convenient than a Yubikey and more secure than SMS. That said, activate an SMS 2FA, if that is the only method of 2FA the application offers. A 2FA with SMS is better than just a password.
I had discussed the flaws of SMS and Soft token authentication factors to give you a perspective of what’s possible as far as bypassing 2FA is concerned. Remember, the attacks discussed are hard to execute. Don’t underestimate the added layer of security 2FA offers.
💡Securing your account with 2FA is not an excuse to have weak passwords. Use a password manager to generate lengthy, complex, and secure passwords. Michael Bazzell of IntelTechniques, recommends password managers - KeePassXC and Bitwarden.
🏃♂️Where to next?
And hey, by the way, please do give FourZeroThree a shout-out to your friends and colleagues, would you? Would really appreciate it! Cheers and happy reading :)