What you could do if your credentials are breached
Malicious cybercriminals are incessantly trying to find ways to breach websites.
If you think your credentials (email addresses, passwords, usernames) were never (or will never be) breached, think again. At least, that’s what you want to think, deny the fact that bad things could happen to good people. I hate to break it to you but data breaches are happening left & right. Malicious cybercriminals are incessantly trying to find ways to breach websites. Some big names that were breached in the past include Linkedin, Quora, Zomato, Equifax, Dubsmash, Zynga, Yahoo, and many more.
Passwords are a necessary evil as far as our increasingly connected lives are concerned. Yet with data breaches exposing more than 4 billion records, including passwords, during the first six months of 2019, they are also a weak link when it comes to security. There is a booming criminal trade across dark web markets in compromised login data.
- Davey Winder (Has your password been stolen? Here’s how to find out)
Being aware of this could cause a certain amount of anxiety or worse, cause panic if you know your credentials were actually breached. But, you know what? Don’t fret. Here’s what you could do to limit the damage done.
🎥FourZeroThree - YouTube
A quick shout out! Here's a “video version” of the article. If you are the visual type, I recommend watching the video. I bet you’ll enjoy it :)
How do you know if your data has been breached?
Here’s what you could do to find out if your private information has been exposed.
💡Have I been pwned?
Troy Hunt has created a fantastic resource called “Have I been pwned? (HIBP”) where you could check if your online account has been breached.
You simply key in an email or password that you used for registering to applications/websites in the past. HIBP would tell you if your credentials have been exposed. In addition, it also gives you the list of the applications/websites you registered to, that were breached.
And if you are not comfortable keying in your real email or password, be rest assured that HIBP does not store your email or password in their database. Also, the credentials you key in to HIBP cannot be connected to you.
💡Firefox Monitor
Firefox Monitor is an online service developed by Mozilla. Like HIBP, it warns you if your email address has been exposed in an online data breach.
Also, you could click on the “Breaches” tab/menu option to get a huge list of breached applications and websites. You could check to see if any application you registered to in the past, has been listed in the breach data.
But you cannot solely rely on the availability of breach data to check if your credentials have been exposed. Companies, at times, don’t immediately realize their database has been breached. It may take many months or sometimes years before the breach is made public. In such cases, there is very little you can do.
💡What could save you or rather, minimize damage when you are unaware of a data breach, is your internet hygiene, which I’ll discuss subsequently.
💻Suspicious activity on your application/website account
There are times when suspicious activities on your email or application accounts could trigger a warning sign of a possible account hack/takeover.
Applications that have fairly robust security, would send you emails (to your registered email address) if they detect a login from a different browser, device or IP address.
You could be locked out of your account because of a password change by the malicious actor. In such a case, you know you have been pwned!
📩Suspicious activity on your email account
This is by far, is the worst thing that could happen. Your email address is sensitive information and is very important to protect, especially if you primarily use a single email address to sign up everywhere. Most websites/applications use services like email, to help reset passwords. If your email is hacked, it is game over! The problem primarily arises when users use the same password (they use for other services) for their email accounts too.
Sometimes, what bad actors could do with hacked email accounts is rather insidious. They tamper with the email service provider’s settings and rules to maximize their benefits. Let me explain with Gmail as an example.
This brilliant insight was explained by Michael Bazzell in this episode, in his podcast, “Privacy, Security and OSINT”.
Bad actors could create new filters in your Gmail account and make your Gmail service forward mails to their email address. This saves them the hassle of repeatedly having to login to your email and triggering an alert. If I am a bad actor, this is what I would do.
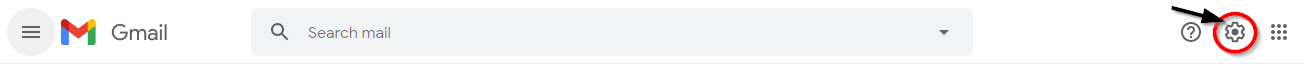
Go to your Gmail settings.
Click “Filters and Blocked addresses” and click “Create a new filter”
Type in your bank’s email address in the “From” filter option and click on “Create filter”.
I would now, set some rules. I could make all mails coming from your bank go to your archives (so the mails don’t appear in your “Inbox”. You could see them only if you clicked the “All Mail” option). Or, even better, I could make your Gmail service forward all mails coming from your bank to my (bad actor’s) email address.
If ever you have a hunch or a gut feeling that something might be wrong, check your filter settings and rules in your Gmail account to make sure everything’s right. If there are unwanted filters and rules, chances are high that your email account has been compromised.
📩Phishing Emails
Your email being breached also means you would be a target to phishing attacks. If you regularly receive a lot of junk/spam or phishing emails, there are chances your email is exposed.
Actions you could take after a data breach
The first thing you should do is to change your password (duh!). Good for you if you didn’t use this password elsewhere. If you did, double down and change this password across all applications/websites you use.
If you are locked out of your account, change your password immediately via the “Forgot Password” functionality (usually present on the “Log in” page of an application). Every application these days possesses one. However, it is possible that the malicious actor would have changed your registered email address along with the password so that you are permanently locked out of your account. The only possible solution then, is to contact or reach out to the support team of the application/company and explain the same.
When changing your passwords across applications, take the pains to also change the registered email address for each application. Preferably create new email accounts and register these new email addresses across all applications.
If there are suspicious filters and rules in your email account settings, delete all of them, change the password of your email account and activate 2FA. Alternatively, create a new email address and delete this one.
Activate 2-Factor Authentication (2FA) wherever possible.
Internet hygiene habits that could minimize damage
Create lengthy, random and complex passwords or passphrases. Usually passwords are exposed as hash values (not plain text). Lengthy and complex passwords are very difficult to crack. So, even if your password is exposed, you minimize damage. You could read more details about this here.
Never reuse passwords, however complex and lengthy they might be. You never know when a website/service (you registered to), would be hacked and your credentials breached! Chant this mantra - “I will use a unique password for every service I use on the web”.
Do yourself a favor and use a password manager.
Secure your account with 2FA wherever possible, especially your email, banking, shopping, and social media accounts.
Do not register to services/websites with your personal email address. Have separate email accounts for personal use, banking, social media, shopping as well as junk/random websites.
You could create burner email addresses/aliases on the fly and use them to register on websites, without risking giving away your real email address.
Regularly use haveibeenpwned to check if your credentials have been breached. Better, subscribe to its services so that you’ll be notified of a breach.
Be alert! Check your email everyday. If ever you receive an alert of a suspicious sign in, take immediate action.